By: Jennifer Adams
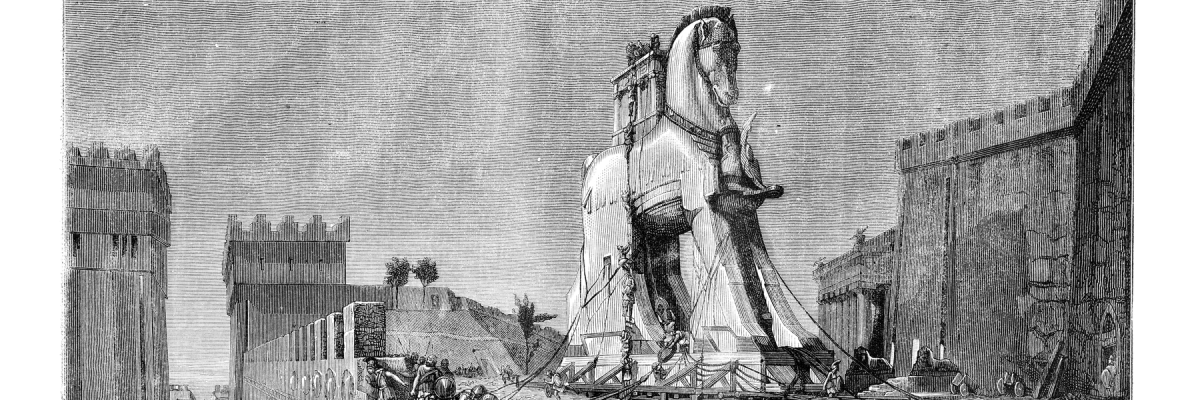
Just like the Greeks were able to gain access and take the city of Troy by hiding soldiers in a giant wooden horse gifted to them so they could gain access and attack, hackers use trojan horses to trick you into inviting them into your network. Here are a few different kinds of trojans, how to spot them so they do not infect your network, and what to do if you believe one is on your computer.
What is a Trojan Horse?
A trojan horse is a form of malware, a program disguised as a legitimate software, designed to breach the security of a computer system. Hackers utilize trojan horses by sending them by phishing or sending emails with an offer that sounds too good to be true, with a link for you to download. Because trojans require user permission to run, hackers try and trick you into clicking on it. If the link is clicked, then the software will download, and your computer will become infected with malware. This allows the hacker to monitor your activity, alter your files, steal your private information and possibly hold it for ransom. Even if the ransom is paid, there is no guarantee your files will be returned or that the information will not be leaked or sold. The easiest way to avoid trojan horses is to be mindful of links and software downloaded. When in doubt, don’t click on any links. Call the sender to confirm the email really came from them or consult a managed IT provider.
What are the different kinds of Trojan Horses?
There are several types of trojan horses. Each type allows hackers to infect and control your computer and steal different information in different ways.
- Backdoor Trojans – The trojan creates a “backdoor” entry, an inconspicuous way for the hacker to not only access your computer but take control of it.
- ArcBomb Trojans– These trojan horses are designed to freeze or slow the system down tremendously once unpacked into the system.
- Banking Trojans – It’s all in the name. Banking trojans are designed to steal confidential data such as banking information, usernames, passwords, and SMS authentications.
- Clicker Trojans – Created to access internet sites and servers, these trojans are inconspicuous so users are not aware as clickers send commands to browsers. Clickers increase website traffic volume in order to get more money from ads, run DDoS attacks, and redirect visitors to web pages containing scams and possibly malware.
- DDoS Trojans – A DDoS attack is successful when a massive number of denial-of-service attacks targeted at a victims IP address overload it and it ceases to function. These types of attacks are like a virus because in order to affect another computer, other devices must first be infected so that a large number of infected devices can target the next device.
- Fake AV Trojan – Fake AV (or fake antivirus software) impersonates real antivirus software in order to extort money from the user mostly from inexperienced users. When a threat pops up, fake AV demands money from the victim to remove threats whether they are real or fake.
- Notifier Trojans – Notifiers are used to send the developer information on the computer, including information from open ports.
- Mailfinder Trojans – Mailfinders are a trojan that steals the email addresses from the infected computer so that hackers can send spam and phishing emails to more potential victims.
- Password Stealing Trojans – PSW trojans can search for passwords stored in files or web browsers as well as software licenses.
- Proxies – Proxies allow hackers access to websites by remotely using the victim’s computer. Once they are in, they send out spam while hiding behind the victims IP address.
How do I tell if my computer is infected and what do I do if it is?
The easiest way to tell if your computer has been infected with a trojan horse is if you notice any new applications on the start-up menu, sudden screenshots, the computer making sounds or displaying photos without you doing so, and sudden rebooting. Consult with a managed IT professional about the best choice of software to guard against these attacks and to monitor your network against potential attacks.
Sources:
https://us.norton.com/internetsecurity-malware-what-is-a-trojan.html
https://www.britannica.com/topic/Trojan-horse
https://www.webroot.com/us/en/resources/tips-articles/what-is-trojan-virus
https://usa.kaspersky.com/resource-center/threats/trojans
https://www.csoonline.com/article/3602790/17-types-of-trojans-and-how-to-defend-against-them.html
